Nowadays, it is more important than ever to know who and when gets access to your properties. In the post-COVID world, there is a growing need for the right solutions to manage office visitors due to the special challenges associated with tracing contacts and reducing the risk of close contact in public places. Moreover, flexible scheduling means employees are more likely to be in the office at unpredictable times, prompting remote control, building automation, and more.
In this article, we are going to discuss a visitor management system, its types, features, benefits, and the way it works. Let’s dive in!
Table of Contents
- 1 What is a visitor management system?
- 2 Types of VMS solutions
- 3 How visitor management system works
- 4 Why use a visitor management system
- 5 How to build a visitor check-in management system
- 6 Crucial features of the visitor management system
- 7 Challenges of biometric visitor management system development
- 8 Tech stack and requirements
- 9 Cost of visitor management system development
- 10 Our experience
What is a visitor management system?
A visitor management system is a technology that keeps track of visitors entering your office. These visitors could be your client, courier, interlocutor, contractor, consultant, or maybe your CEO’s grandmother’s cousin. The point is, anyone who enters the building is a visitor.
This system replaces the usual visitor record with a more accessible medium. It gives you access to monitor a visitor who enters your buildings, campuses, or other facilities.
During the COVID-19 pandemic, more and more important industries are turning to visitor management systems to help them safely adapt to the safety challenges of their workforce, while continuing to provide products and services that, in some cases, are even more in demand. These include schools, universities, malls, manufacturing companies, data centers, pharmaceutical companies, food manufacturing and packaging, chemical companies, etc.
Types of VMS solutions
Internet technologies have developed by leaps and bounds during the first two decades of the 21st century, and at a faster pace than in the previous 50 years. Although the role of the receptionist has changed dramatically, some companies continue to use pen and paper as their standard visitor management system.
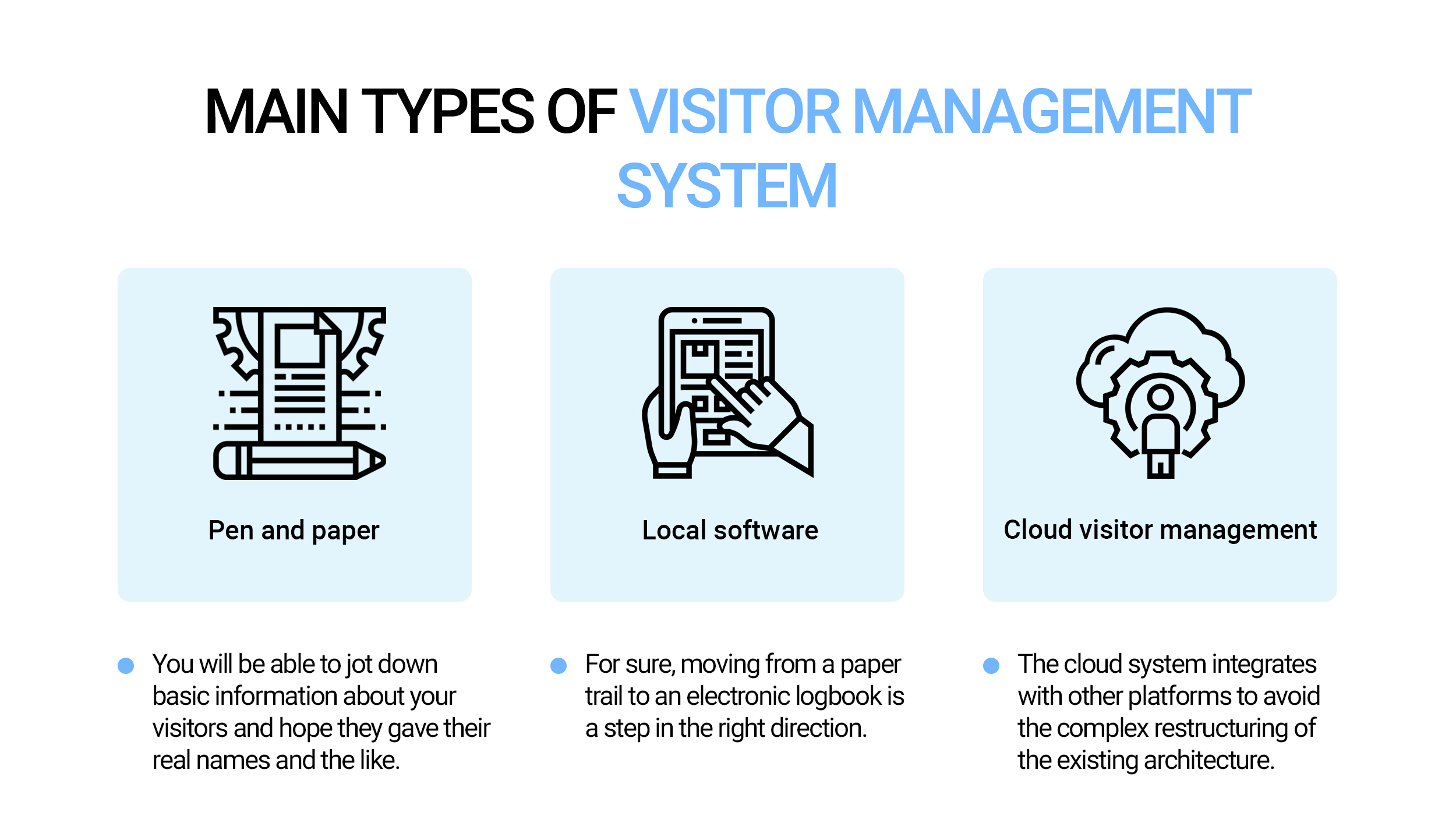
Pen and paper visitor management system
The infamous paper magazine – what seems like a fairly innocent and inexpensive VMS can end up costing you more in the long run. You will be able to jot down basic information about your visitors and hope they gave their real names and the like. But that is if you can read their handwriting at all. But in terms of efficiency and safety, you are asking for trouble if you rely on a paper logbook. Visitor entry tables not only cause long queues at the check-in counter but also violate the privacy of your visitors as their information remains in full view of the next person.
Local software
For sure, moving from a paper trail to an electronic logbook is a step in the right direction. But do you want to deal with the amortized cost of legacy systems? Plus – knock on wood – in the event of an emergency or evacuation, this “electronic entry sheet” stored on your hard drive in your office won’t do you the same good as a cloud-based visitor management system.
Cloud visitor management
The interface is connected to the cloud, where information that visitors enter is collected and then displayed – on the other side of the check-in counter – in a dashboard for easy management. Moreover, the cloud system integrates with other platforms to avoid the complex restructuring of the existing architecture (and many common problems with the introduction of new technologies). Only a cloud-based SaaS solution can provide you with a best-in-class approach so that you have more control over what you use and what you pay for.
How visitor management system works
When using an electronic visitor management system, visitors log into the system using a computer rather than a paper login sheet. Upon arrival, the visitor informs the administrator of his name. The administrator then enters the visitor’s name into the computer and prints out a temporary visitor badge, which is then issued to the visitor. When the visitor leaves, he or she returns the visitor’s badge to the administrator, who then signs the visitor on the computer.
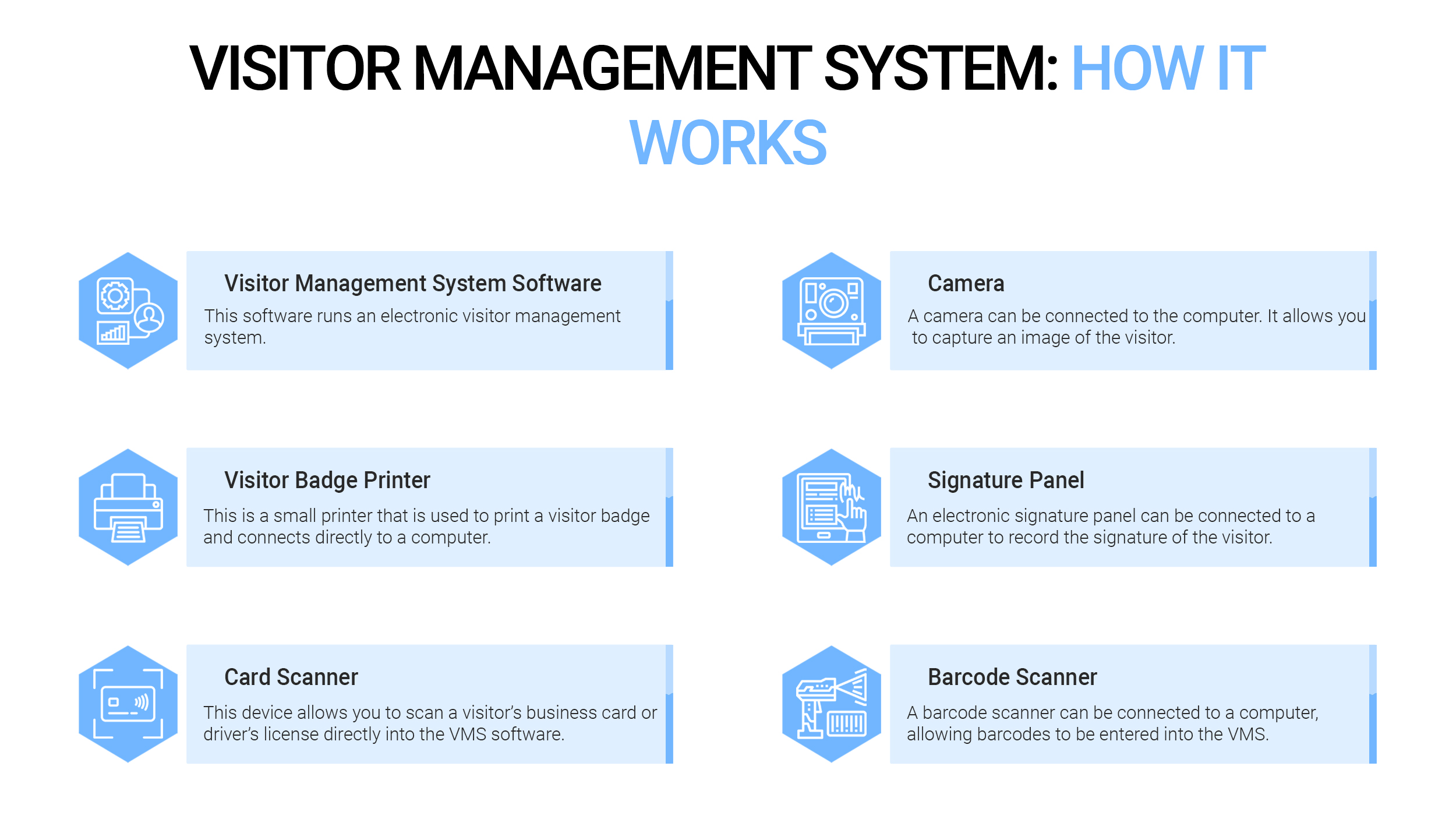
This software runs an electronic visitor management system. Most institutions will install this software on an existing personal computer that is already located at the reception desk.
☑️Visitor Badge Printer
This is a small printer that is used to print a visitor badge and connects directly to a computer running the visitor management system software.
☑️Card scanner (optional)
This device allows you to scan a visitor’s business card or driver’s license directly into the visitor management system software. This speeds up the registration process of visitors and increases the accuracy of the information entered. When scanning a driver’s license, the system can also take the picture shown on the license. If desired, this picture can be printed on the visitor’s badge.
☑️Camera (optional)
A camera can be connected to the computer. It allows you to capture an image of the visitor using the visitor management system software. If desired, this picture can be printed on the visitor’s badge.
☑️Signature panel (optional)
An electronic signature panel can be connected to a computer to record the signature of the visitor. This is often useful when a visitor must sign a non-disclosure agreement or confirm a security policy before being allowed to enter a facility. If desired, the signature of the visitor can be printed on the visitor’s badge.
☑️Barcode Scanner (optional)
A barcode scanner can be connected to a computer, allowing barcodes to be entered into the visitor management system. By scanning the printed barcode on the visitor badge, visitors can quickly log out as they leave the facility. This scanner can also be used to log in visitors who have pre-registered and received a printed visitor confirmation email containing a barcode.
Why use a visitor management system
An electronic visitor management system offers the following advantages over the traditional manual visitor entry process:
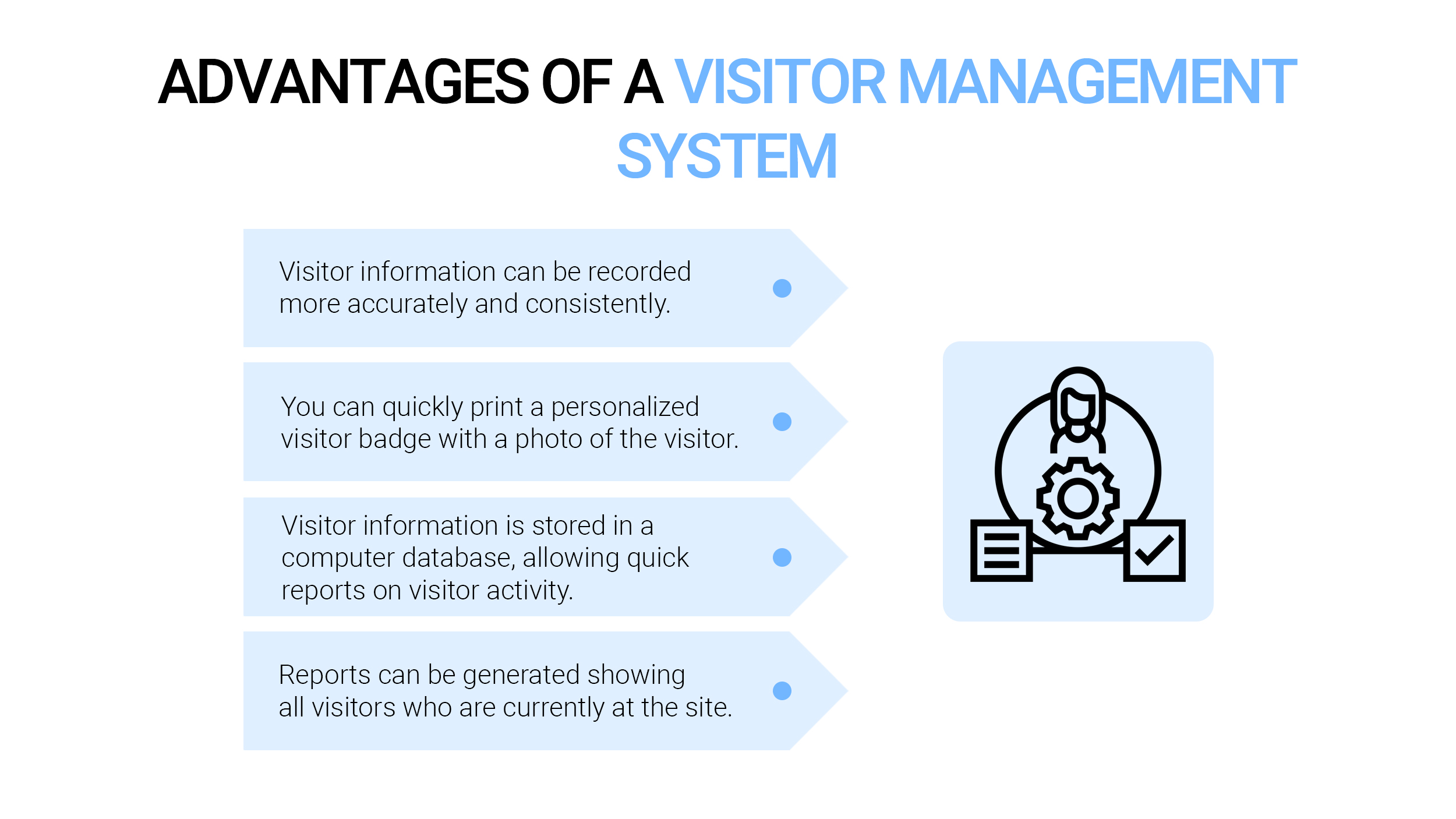
- Visitor information can be recorded more accurately and consistently.
- You can quickly print a personalized visitor badge with a photo of the visitor.
- Visitor information is stored in a computer database, allowing quick reports on visitor activity. These reports can be used to find out how many times each visitor has logged in and out and when, and to see which visitors have been at a facility during any given time. This information can be useful when investigating security or security incidents, and when checking invoices issued by suppliers or contractors.
- Reports can be generated showing all visitors who are currently at the site. This can be useful during emergencies and evacuations.
- Visitor information can be stored in the system, allowing returning visitors to log in quickly in the future.
- Visitors can be pre-registered with the system, which speeds up the login process when a visitor arrives.
- If photographs of visitors are taken, the photographs can help investigate security incidents that may have occurred while the visitor was on the premises.
How to build a visitor check-in management system
Visitor management system development consists of several steps. Below we’ll discuss the main ones.

Before embarking on the development and design of a VMS, it is necessary to determine the system requirements for the elements that are used in this project. The VMS system requirements are configuration, feature and data requirements, and laptop quality limits. The goal of the system requirements is to keep the VMS running smoothly and efficiently to make the registration process faster and easier.
2. Graphical user interface
In general, the graphical user interface is intended to provide the user with a comfortable and intuitive environment that does not require complex methods to display information and control the manipulator. It is necessary to design and develop an easy-to-use interface in the VMS so that it can facilitate the registration procedure and process.
3. Database management system
VMS requires its database management system to record all visitor logs and information when they check in to the face counter. A database management system (DBMS) is a system software capable of collecting and managing the database of visitors.
4. System integration
System integration is an important step for every system, especially for VMS. It consists of a process that iteratively combines subsystems of components into one system. In addition, it is also mostly implemented for consistent levels of the system hierarchy.
5. Real-time testing
After the design of the entire VMS, real-time testing needs to be done to detect errors and system failures. Typically, real-time testing is a trial and error process that is useful for testing complete and integrated systems.
6. System implementation
At this stage of implementation, the VMS can be created after several stages of real-time testing. Therefore, it is important to ensure that the VMS meets the quality standard.
Crucial features of the visitor management system
What features should you pay attention to when choosing a modern visitor management system for an educational institution? It is worth focusing on the capabilities that will solve the main tasks of the update, namely security, convenience, or both at the same time. Below are some of the additional items to include in your checklist.
Sign-in and sign-out
Visitors should be able to quickly and easily add their information using a keyboard or touchscreen. Digital inputs are faster and eliminate the confusion, redundancy, and potential for errors that can occur with handwritten logins. The exit should be very simple, ideally with a single button.
Custom login processes
Visitor entry requirements may vary depending on the type of visit. For example, the process of registering a delivery person can be very different from the process of registering a person who comes for an interview. Your employees may also want to let some VIPs skip most of the login process or pre-register them so they don’t get stuck signing the same legal documents that other visitors are required to do, for example.
Data storage and reports
All visitor registration data must be kept in a safe place. Employees should be able to generate reports on this data to gain valuable insight into how the front desk is performing. In particular, a quick report that lists everyone present in the office at any time can be useful in the event of an emergency evacuation. These reports should be easy to sort, filter, export, and publish. If your company must adhere to certain security protocols, you can build in something to delete visitor data after a certain number of days.
Signing the document
The best visitor management systems integrate document signing into the registration process and securely store an electronic version of these signed records on the Internet. The system should guide the visitor through a streamlined process that includes any signatures.
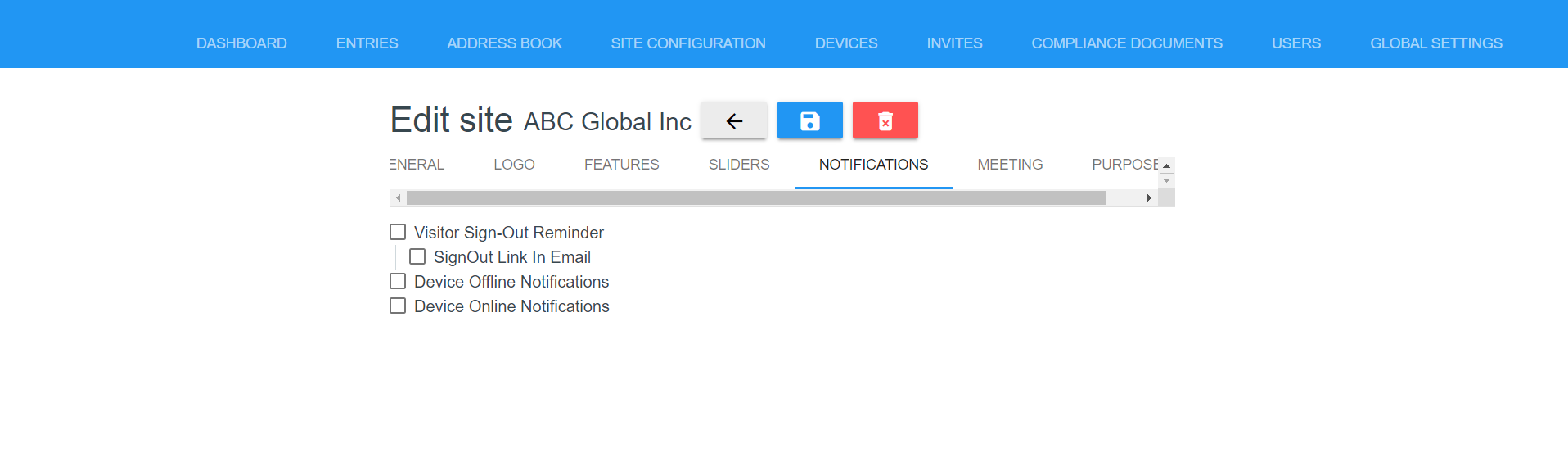
Staff notifications
Visitor management systems should have a notification system that alerts employees when someone who wants to visit them is logged in. Ideally, employees should be able to choose what types of notifications they want to receive and when.
Easy integration with the printer
You should be able to print guest badges immediately and without delay. This is an essential feature no matter what kind of icons you want to print. You can opt for badges that fit in reusable laces, in which case you just need a high-resolution printer that works in a small format. This is especially important if you want to use barcodes on your badges. In other cases, it is better to use a sticker printer that creates temporary guest badges that can be attached to shirts without a string.
Ability to use photos and barcodes
What decorates your badges? The name may be enough for some guests. In high-security situations, he can pay to print photos and unique ID barcodes. This will allow you to more effectively track people as they move around the school, noting when they are checked in and out by scanning a barcode, and ensuring that anyone who comes across them can verify the identity of visitors right away from their photographs.
Communication with other management software
A convenient way to export visitor data to a more centralized database is a big advantage of using a modern digital visitor management system. Without the step of manually importing content from written journals into the system, there is less room for human error and less time spent by administrative staff.
Challenges of biometric visitor management system development
Probably, the biggest problem with a successful tracking and tracing application is user acceptance. Identity issues, motivation to use, and general security concerns all create a problem – even before the app even gets into the development phase. Without adequately addressing security concerns and demonstrating robust security controls, application adoption can fail. Here is the list of the main challenges.
✓Hardware
The application must run on hardware designed to solve the problem or use a variety of mobile devices already available.
✓Identity
The user and his environment must be presented anonymously and securely. Failure to protect an individual will negatively affect acceptance.
✓Proximity
The app must be able to recognize meetings with other phone users. Again, security issues need to be addressed with this feature.
✓Communication
Data must be transmitted and processed securely.
✓Motivation
Users must trust the app to use it. Without user confidence, the motivation to download it will be negligible.
Tech stack and requirements
Creating a good visitor management system requires the right technology. So, below we have listed a technology stack that will help you move forward.
| Front-end | React.js/Angular |
| Back-end | Node.js/Loopback/Laravel |
| Application | React Native |
Cost of visitor management system development
The final price of a visitor management system depends on many factors. Here is the list of the ones that influence the most: the complexity, size of the team, the developers’ location. If you want to see the more precise cost, you can follow the table below where we have mentioned the approximate time it takes developers to build applications. Take a look!
| Scope | Approx time, hours |
| 1. Project Start | |
| Initial backlog preparation | 10 |
| Project Schedule Preparation | 10 |
| Staging environment setup | 6 |
| 2. Back-end | |
| Communicate with API that retrieving data from the CCC platform | 0 |
| Integrate Evoke API | 0 |
| 3. Front-end | |
| Project set up | 10 |
| UI components (button, header, inputs, cards, list, screen, animations) | 32 |
| Splash screen | 4 |
| Welcome | 3 |
| Wallet Pass | 7 |
| Home | 6 |
| Text Verification | 5 |
| Log a visitor | 8 |
| Packages | 3 |
| Announcements | 5 |
| Service Requests | 8 |
| Verification screens | 5 |
| Visitor without vehicle | 7 |
| Visitor with vehicle | 8 |
| 4. Stabilization and Delivery | |
| Prepare deployment docs | 8 |
| Prepare description docs | 8 |
| Production deployment | 17 |
| 5. Project management | |
| Backlog elaboration and maintenance | 12 |
| Planning meetings, review meetings | 9 |
| Project Management and communication | 9 |
| Quality Assurance, hours: | 33 |
| Total Development, hours: | 134 |
| Project Management, hours: | 216 |
| Total: | 216 |
Thus, the cost of a visitor management system creation depends on the complexity of the project and its features. To get the detailed estimation contact us via email: andrew.gromenko@code-care.pro.
Our experience
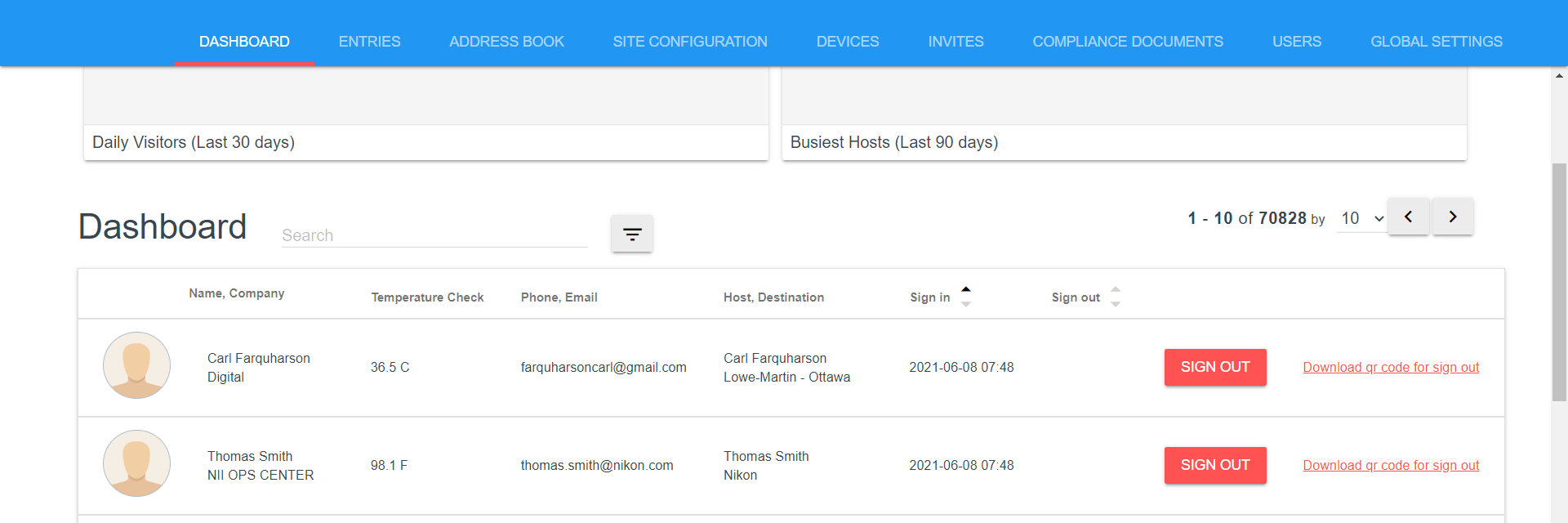
The Code&Care team has wide experience in visitor management system app development. The most prominent project is MyLobby. First, it was created to provide an easy and efficient way for businesses of all sizes to manage their visitors and contractors entering a building. Now, they have expanded into medical examinations to help people lead healthier lives at work.
To bring the project to life, our developers used the list of technologies. Such as Angular and React.js for front-end development, Node.js, and Loopback for back-end, React Native for application development.
To make a visitor management system comfortable for customers we implemented a wide list of features:
☑️Contactless COVID-19 compliance
Everyone uses a QR code to identify themselves.
☑️Face recognition
Employee face recognition integrates with door access control.
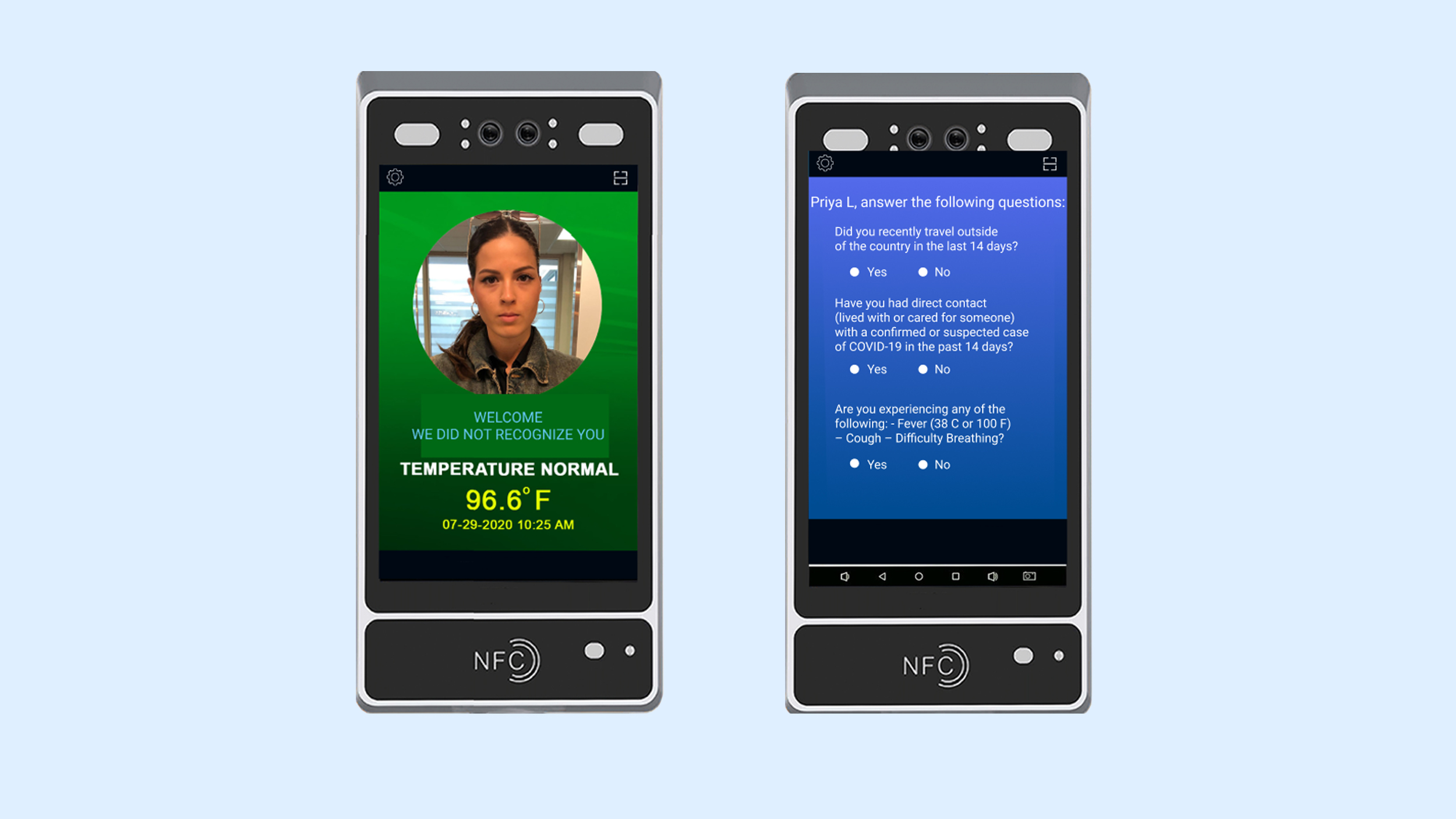
The platform allows companies to customize COVID-19 questionnaires on the fly at any time to suit your organization’s needs.
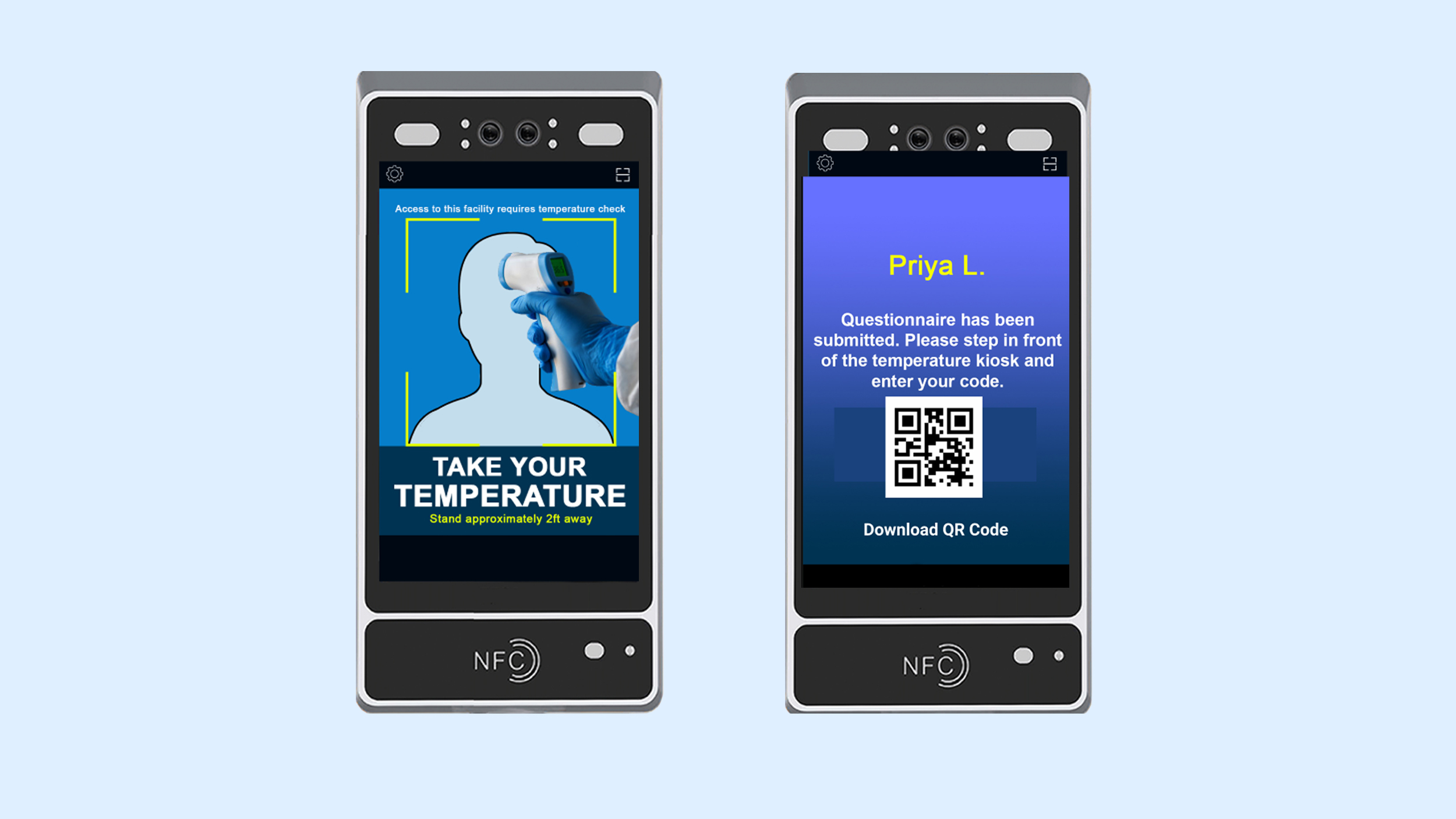
☑️Onboard temperature calibration
Built-in temperature calibration ensures accurate temperature readings.
☑️Time and attendance of employees
Lots of functions as employees check. Pull reports track wait times. API integration with other payroll systems.
With your own NFC card or key fob, you can log in and get a temperature scan within seconds.
☑️QR code login capability
QR codes allow employees and staff to easily enter the system without touching the temperature scanner.
☑️Temperature scan
Scan the temperature of visitors and staff entering the facility.
There is the opportunity to turn on the photography option, which will automatically take a picture of your visitor upon registration. Once captured, the image will be added to the visitor log along with other registration details.
☑️Custom printed badges upon request
Visitor badges are printed every time they check-in.
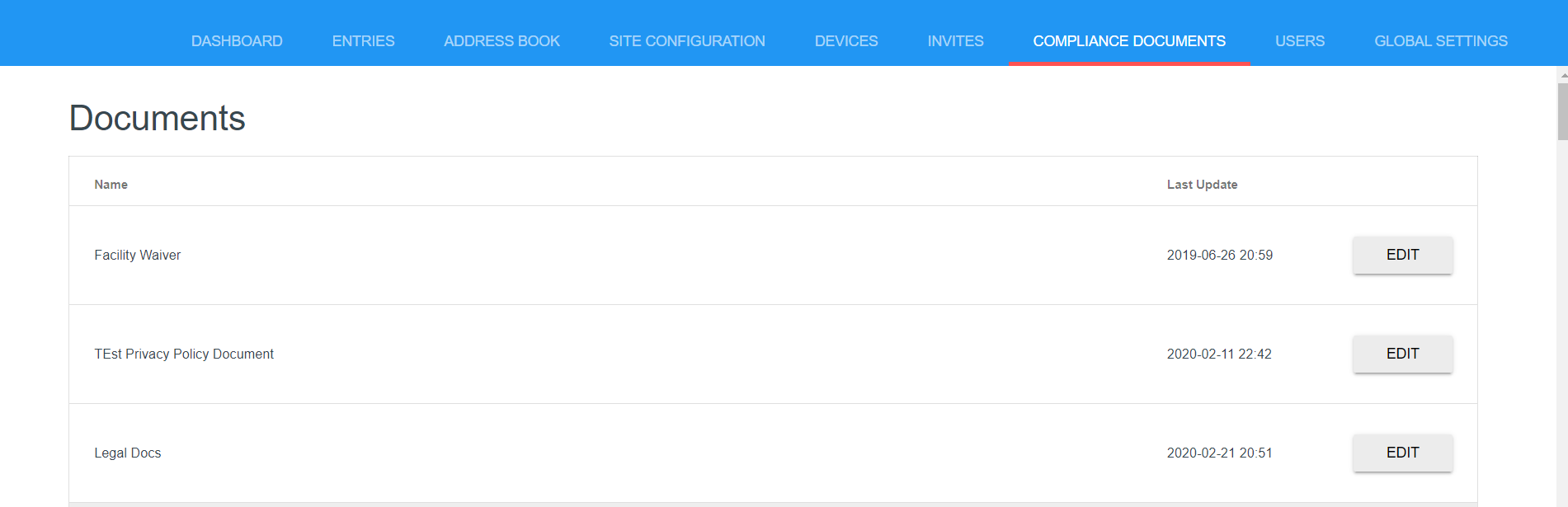
☑️Legal and regulatory documents
Make sure all visitors comply with the property’s requirements.
Send a personalized email and messages to everyone in the building.
✔Related articles:
How to Build a Virtual Event App: Comprehensive 2022 Guide
E-learning application development: Process, Features, and Cost
How to Make an App Like OnlyFans: Features, Steps, Cost
How to Make an App like Clubhouse: Features, Tech Stack, Cost















No comments yet.
Give us your impression about this article.